How teams phase in identity, representation, and authorization
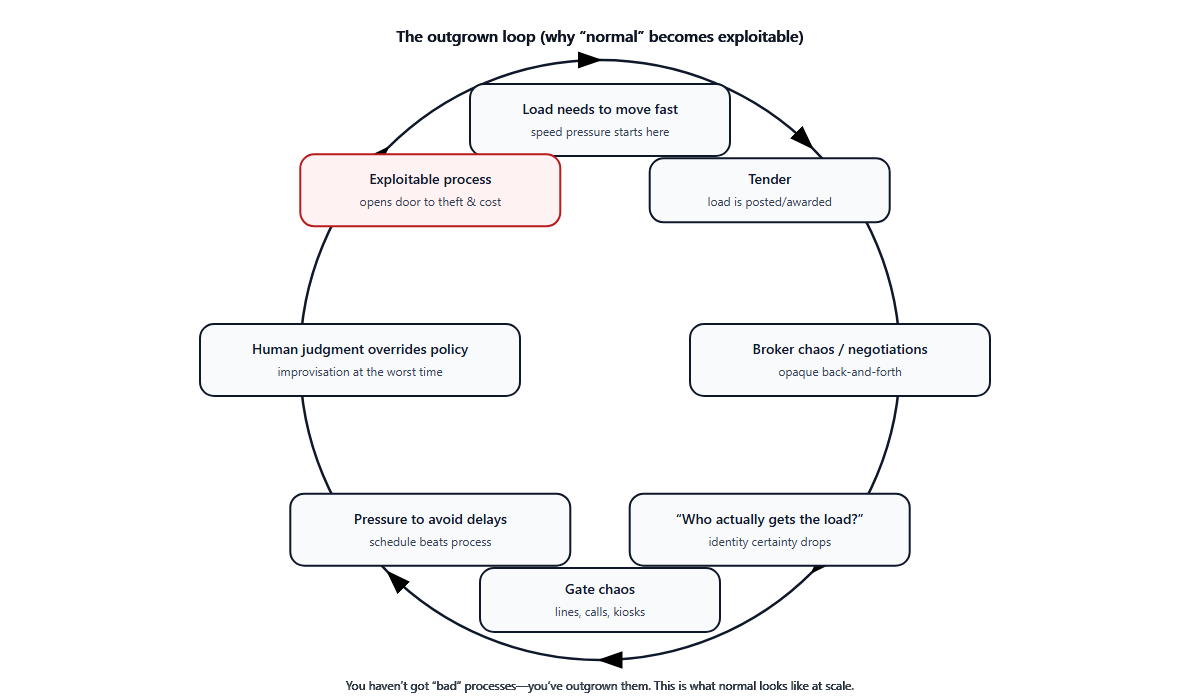
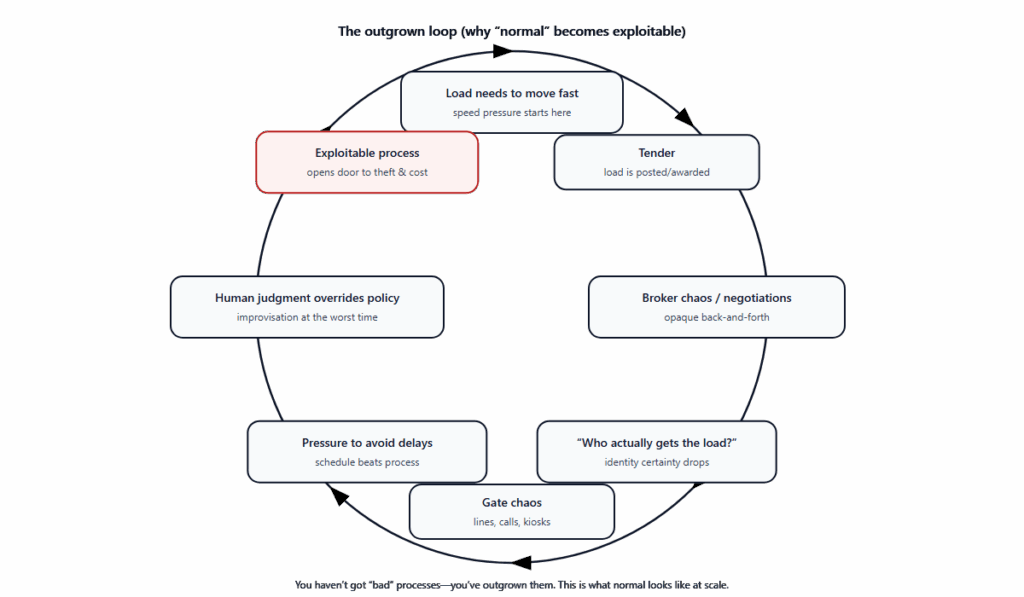
By now, this series has established a clear operational method. Frontline teams should not be asked to perform due diligence under time pressure. The burden of proof should sit with the requester. Decisions should be protected by recording why they were made, not just what happened. Proof should be classified — identity, representation, and authorization — so teams stop guessing. And infrastructure is required to support providing proof.
At this point, most organizations reach the same conclusion: the method makes sense, but adopting it changes how people interact with us.
That’s unavoidable. This approach doesn’t just alter internal workflows. It reshapes expectations for customers, carriers, drivers, brokers, and contractors. Adopting it isn’t a tooling decision. It’s a change-management exercise.
Where teams tend to fail isn’t disagreement with the method. It’s speed. They try to introduce everything at once: authorization rules without context, proof requirements without explanation, friction before trust exists. The reaction is predictable. Partners feel blocked. Frontline feels exposed. Exceptions creep in, judgment quietly replaces proof, and the system reverts to its old shape.
Teams that succeed take a different path. They phase the change.
Most start with identity, not because it solves the problem, but because it’s the lowest-risk entry point. The first requirement introduced is simple: operational requests must be tied to a real, verifiable person before information is disclosed. This builds on work teams already do through onboarding, contact verification, and basic KYC. Execution doesn’t change. No one is blocked from doing their job. What changes is intentionality. Information is no longer shared casually. Identity is no longer assumed. Requests are no longer anonymous.
Identity works as a starting point because it controls information, not execution. Mistakes are recoverable. It familiarizes partners with proof-based interaction and creates muscle memory without disrupting flow. Just as important, teams are explicit about what identity does not do. Identity does not authorize changes. It does not bind companies. It does not replace representation or approval. That clarity prevents overreach.
During early adoption, many teams consciously substitute identity checks for proof that would ideally be authorization. That can be acceptable — if it’s done honestly. In practice, this means allowing identity-verified requests to proceed even when authorization proof doesn’t yet exist, while explicitly recognizing the residual risk. The goal isn’t to pretend the risk is gone. It’s to reduce the most obvious attack surface, gain incremental protection over anonymous requests, and acclimate counterparties to the expectation that proof will increasingly be required.
In this phase, identity functions as a training mechanism, not a substitute. Frontline teams must be coached to understand that proceeding on identity alone still carries contractual risk, that responsibility hasn’t fully shifted, and that this should be acknowledged and documented. Being able to say, “We proceeded based on identity verification alone; authorization proof was not available,” preserves honesty and momentum at the same time. Substitution is safe only as long as the residual risk remains visible. The moment it disappears, the method breaks.
Once identity discipline is in place, a deeper gap becomes obvious. Most organizations already perform company-level due diligence during onboarding — carrier vetting, shipper KYC, insurance verification. But that diligence lives outside daily operations. It isn’t connected to action. So the next requirement emerges naturally: company due diligence must be linked to representation, not just stored at setup.
People stop being “just contacts.” They become representatives acting for a specific company, within a defined scope, in a specific context. This is where routine-sounding requests quietly introduce risk: dispatcher handovers, driver substitutions, “no-change” swaps. Without representation clarity, these are inferred through familiarity and continuity. With it, they become verifiable. This phase bridges the gap between knowing who someone is and knowing what they are allowed to do, and it’s where documentation starts to matter in a concrete way. Representation is asserted. Scope is recorded. Decisions become defensible.
Authorization comes last, because it’s where the method becomes real — and where unmanaged change causes the most damage. The requirement here is explicit: changes that bind contracts must be backed by verifiable authorization that reaches the point of execution. Reroutes, timing changes, equipment swaps, mid-load exceptions all fall into this category.
Authorization has a non-negotiable constraint. It must be tied to a specific load and moment, and it must reach the decision-maker without leaking exploitable information. Frontline operators need to know that authorization exists, that it came from the correct party, and that it applies to this request. They must not be exposed to who approved, how approval was obtained, or which internal relationships can be manipulated later. Knowing that approval exists is necessary. Knowing who approved often creates new attack surface.
Crucially, authorization must not transfer responsibility back to the frontline. Proof satisfies authorization. It does not ask the operator to judge credibility.
Teams meet these requirements in different ways depending on partner size and technical maturity. What matters is the pattern, not the implementation. Smaller partners often operate in a shared decision space where proof exists without being copied, forwarded, or re-explained. Larger partners rely on external attestation, where authorization is asserted and verifiable while internal context remains abstracted. In both cases, execution sees proof, not people, and frontline judgment is removed.
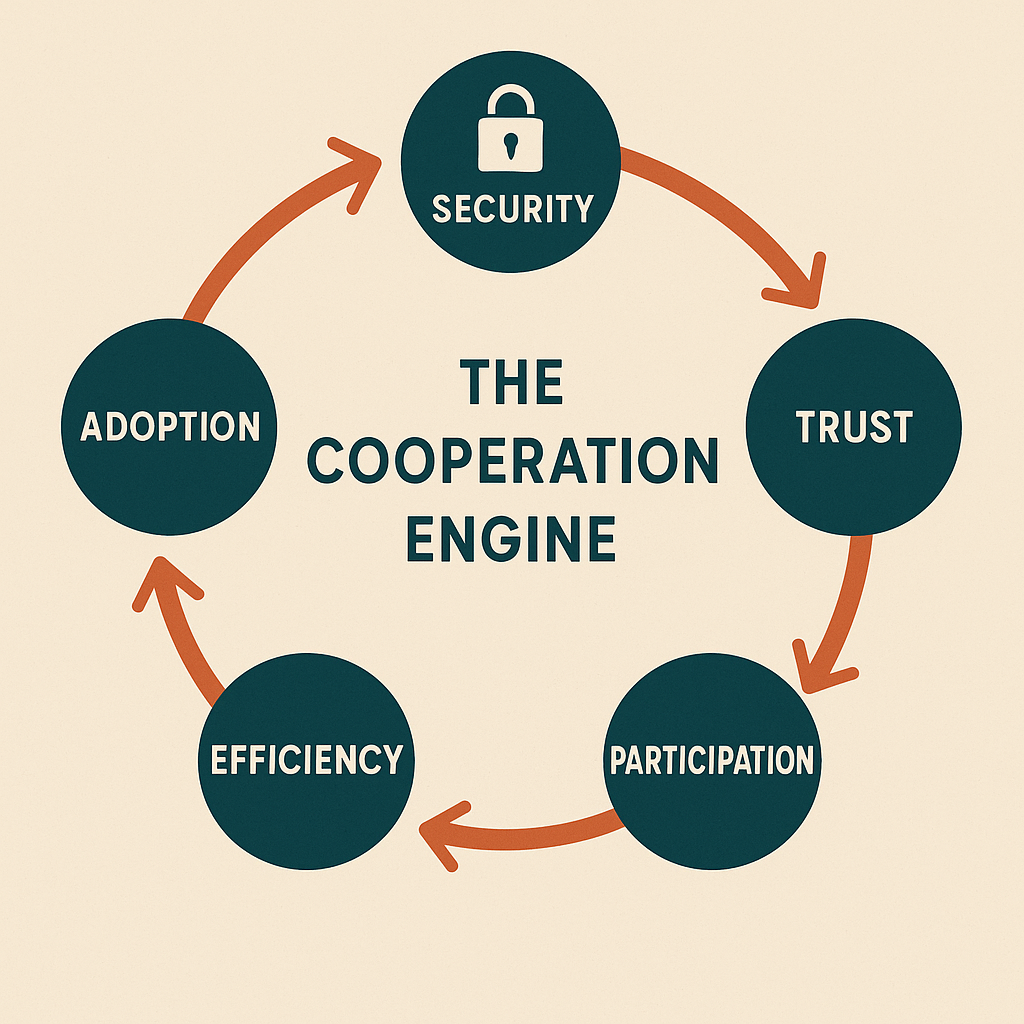
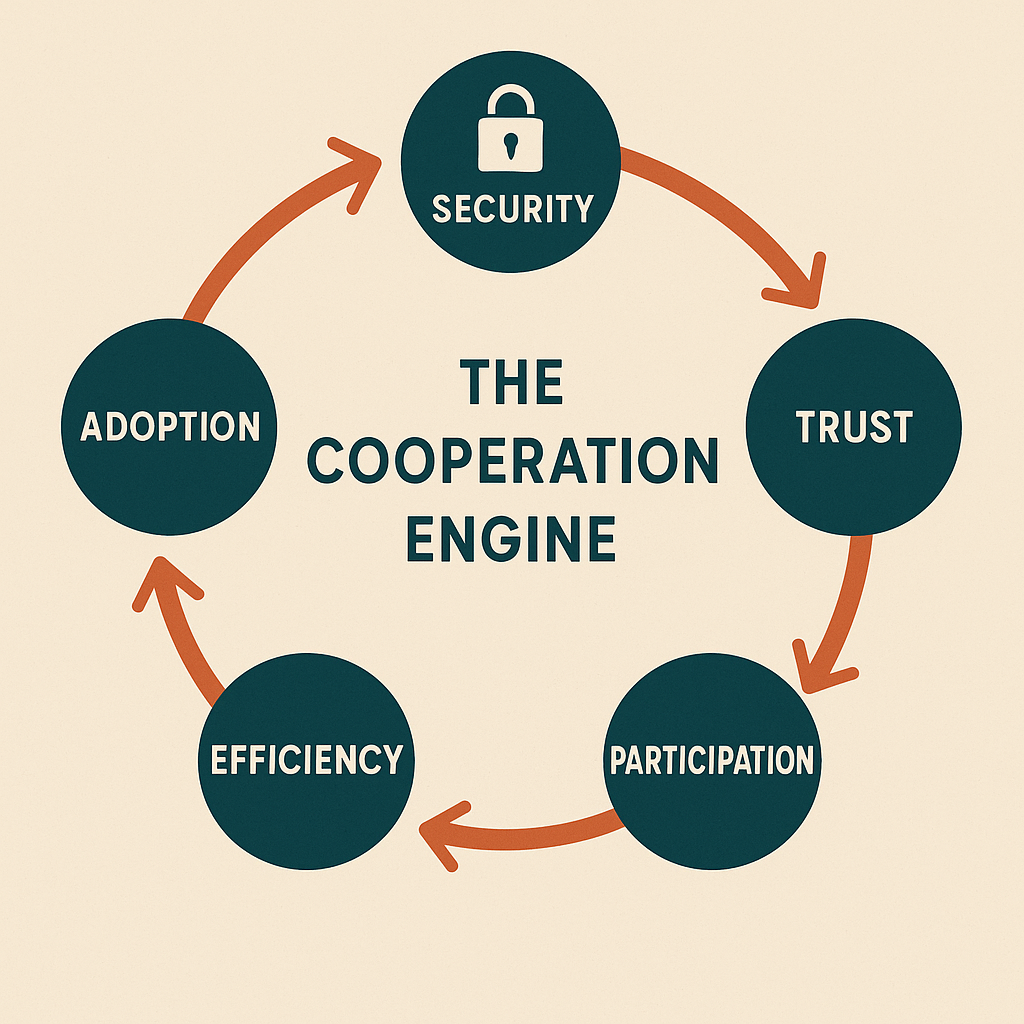
This sequence works because each phase introduces a new requirement only when the organization is ready for it. Identity builds discipline without disruption. Representation links existing diligence to action. Authorization enforces contracts without guessing. At no point is the frontline asked to “be more careful,” and at no point is responsibility silently pushed back downstream. Change is absorbed, not resisted.
Whether teams are retooling, building internally, or evaluating vendors, the test remains the same. If a system requires frontline operators to infer intent, recognize names, judge credibility, or decide whether approval “sounds right,” it violates the method. Not because it’s poorly designed, but because it recreates due diligence under pressure.
Up to now, this series has focused on method. The next entries focus on mechanisms: how identity proof is requested without friction, how representation is asserted and recorded, and how authorization reaches execution without leaking context. Not as features, but as patterns that make this change sustainable.
Because the hardest part isn’t knowing what to do. It’s introducing it without breaking everything else.